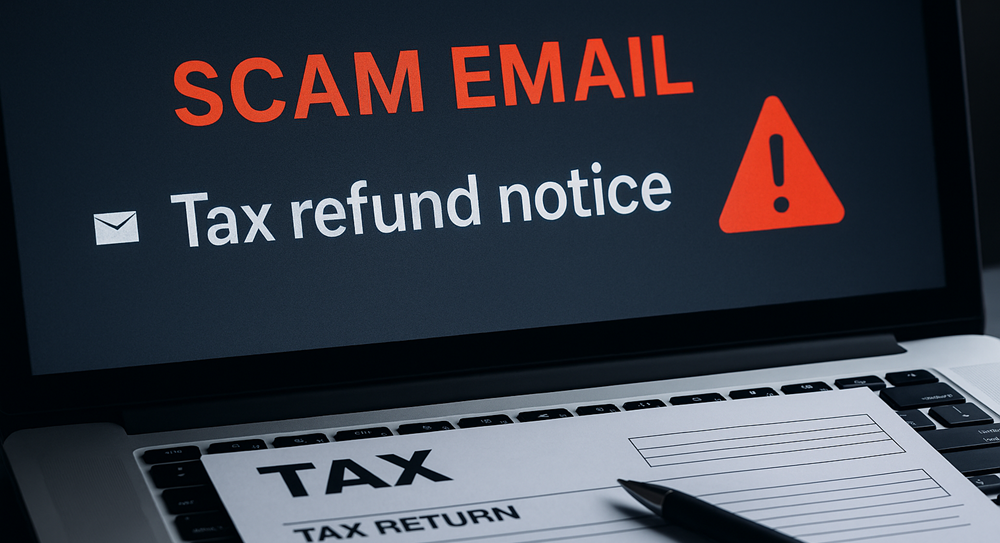
When you replace old computers or external drives, do you delete data and then just… get rid of them?
You could be putting your sensitive data at risk.
A new study by a data recovery specialist shows that millions of deleted files can be recovered from improperly wiped hard drives that are sold online.
It’s not just buyers who can access your old files. Cybercriminals often buy used hard drives and attempt to recover data from them. This could include anything from confidential business information to client details.
It’s easy to forget about old data when you’re excited about shiny new technology. However, it’s important to consider what’s on that old drive before selling it or disposing of it.
Even if the drive is encrypted, it’s still possible for data to be recovered. And if the drive is damaged, there’s a chance that some of the data is still salvageable. It’s better to be safe than sorry when it comes to sensitive information.
Think about it this way: Would you leave important documents lying around for anyone to see? Of course not! Your digital information deserves the same level of protection.
So what can you do to protect yourself?
Don’t let your old hard drives become a liability. Take the time to have them properly wiped or destroyed before disposal. If you’re upgrading hardware, consider hiring a professional to handle the data transfer and ensure that your old devices are wiped clean.
This isn’t just about protecting yourself. It’s about protecting your employees, clients, and anyone else whose personal information you may have stored on that old drive.
It’s a small investment to make for the peace of mind that comes with knowing your data is safe from prying eyes.
Don’t take chances with your data – take action to protect it:
- Properly wipe or destroy old hard drives
- Bring in a professional for your hardware upgrades
- Upgrade your overall security practices
If you need more information on how we can help, please get in touch.